5 PAM Best Practices for Healthcare Cloud Security
Post Summary
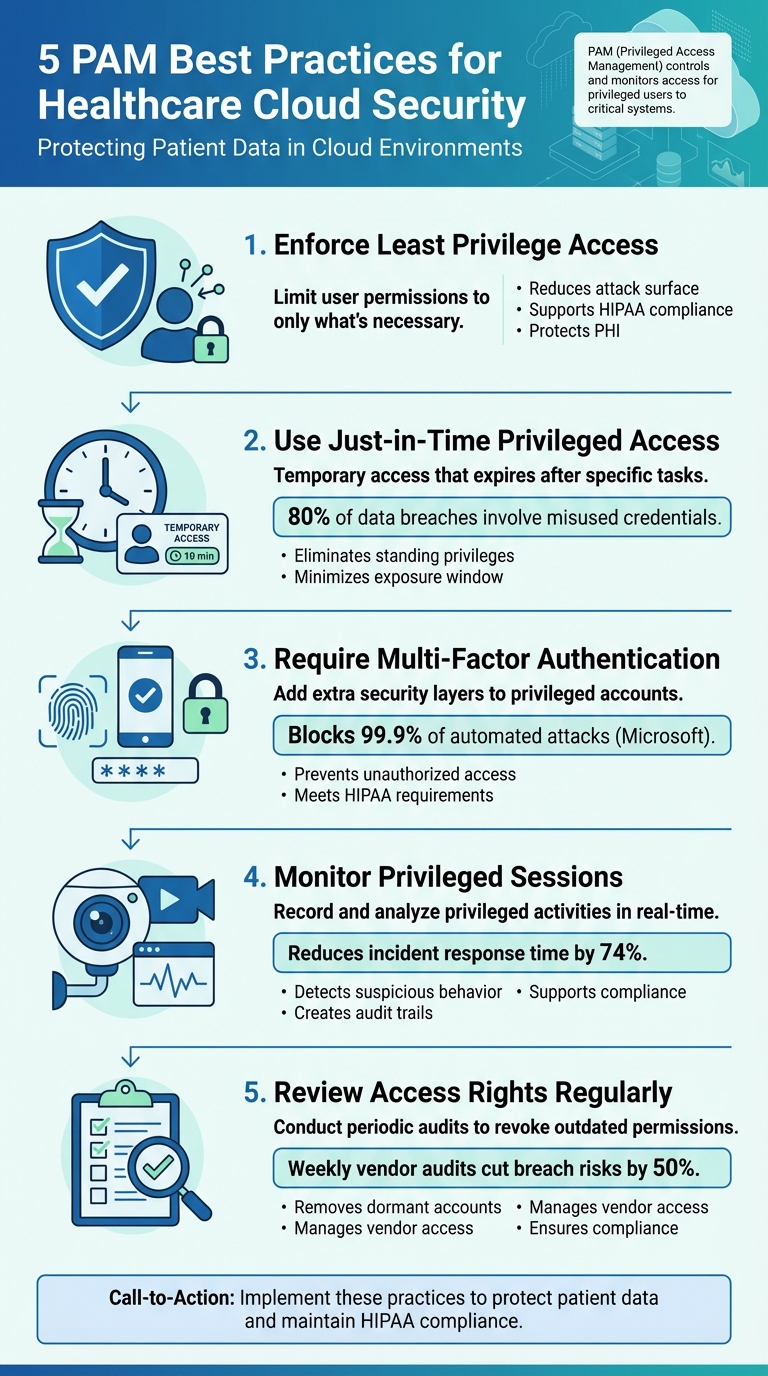
Privileged Access Management (PAM) is critical for protecting sensitive healthcare data in cloud environments. Cyberattacks targeting healthcare systems often exploit privileged accounts, leading to data breaches and operational disruptions. This article outlines five key PAM strategies to strengthen healthcare cloud security:
- Enforce Least Privilege Access: Limit user permissions to only what's necessary for their role, reducing exposure to attacks and supporting compliance with HIPAA.
- Use Just-in-Time Privileged Access: Provide temporary access that expires after specific tasks, minimizing risks from standing privileges.
- Require Multi-Factor Authentication (MFA): Add an extra layer of security to privileged accounts, significantly reducing the chances of unauthorized access.
- Monitor Privileged Sessions: Record and analyze privileged activities to detect and address suspicious behavior quickly.
- Review Access Rights Regularly: Conduct periodic audits to revoke outdated permissions and manage vendor access effectively.
5 PAM Best Practices for Healthcare Cloud Security
Traditional PAM vs Cloud CPAM for a cloud first world
sbb-itb-535baee
1. Enforce Least Privilege Access
The principle of Least Privilege ensures that users are granted only the permissions necessary to perform their specific job functions. In healthcare cloud environments, this approach is crucial for protecting sensitive patient data. For example, a billing coordinator doesn’t need access to clinical imaging systems - so they shouldn’t have it. By restricting access in this way, organizations not only reduce exposure to potential risks but also establish a strong foundation for other security strategies.
Reducing Attack Surface
Implementing least privilege significantly reduces the number of entry points available to attackers. In cloud environments, a compromised administrator account can potentially expose the entire system infrastructure. By limiting access and conducting automated reviews to remove unused permissions, organizations can minimize this risk. If a low-level account is compromised, the least privilege framework ensures attackers are blocked from accessing high-value systems containing Protected Health Information (PHI).
Meeting HIPAA and Healthcare Compliance Requirements
Enforcing least privilege also supports compliance with regulations like HIPAA and Identity Governance and Administration (IGA). It ensures that sensitive resources remain protected and that access is continuously monitored. Under the Shared Responsibility Model in cloud environments, the cloud provider secures platform access, but healthcare organizations must implement internal controls to prevent unauthorized data sharing. Least privilege policies also help meet Data Loss Prevention (DLP) goals by making sensitive data less vulnerable to breaches through strict access limitations.
Protecting Patient Data and PHI
Permanent Role-Based Access Control (RBAC) permissions can introduce unnecessary risk. Instead, organizations should use Just-in-Time (JIT) access, which grants temporary permissions that expire once specific tasks are completed. For instance, a database administrator can authenticate, perform maintenance, and lose access automatically after the session ends. Additionally, dividing responsibilities - such as assigning separate "creator" and "approver" roles for managing patient records - ensures no single individual has unchecked control over sensitive data.
Improving Efficiency in Healthcare Cloud Operations
Applying least privilege through cloud-native Privileged Access Management (PAM) tools not only enhances security but also improves operational efficiency. This approach prevents privilege creep as staff roles change or new infrastructure is added. Real-time monitoring further strengthens security by detecting anomalies, such as repeated unauthorized access attempts, which may signal a compromised account. Addressing these incidents quickly helps maintain the integrity of healthcare cloud systems while keeping patient data safe.
2. Use Just-in-Time Privileged Access
Just-in-Time (JIT) Privileged Access replaces constant administrator rights with temporary permissions that automatically expire. For example, instead of granting a database administrator permanent access to production systems containing PHI, JIT provides credentials valid for 30–60 minutes. This is usually enough time for tasks like rotating encryption keys or applying patches. Once the time is up, access is revoked. This approach pairs well with least privilege strategies by removing persistent access and adding another layer of security to cloud environments.
Reducing Attack Surface
Nearly 80% of data breaches involve the misuse of credentials [4]. JIT significantly reduces the window of opportunity for attackers by eliminating standing privileges altogether. In a Zero Standing Privileges (ZSP) model, accounts have no ongoing access to sensitive cloud resources. This minimizes exposure across thousands of cloud actions in platforms like AWS, Azure, and GCP [4]. Instead of relying on static keys or tokens that can be exploited, JIT issues short-lived credentials, reducing the risk for APIs, bots, and service accounts.
"If you had to pick a single control that changes the game for cloud security, you might want to choose killing standing privileges." - Cloud Security Alliance [4]
By limiting access to short, specific timeframes, JIT not only improves security but also simplifies auditing processes.
Meeting HIPAA and Healthcare Compliance Requirements
JIT strengthens Privileged Access Management (PAM) strategies by ensuring that all access is both time-limited and justified. Each JIT session generates a detailed audit trail, documenting who requested access, what they were allowed to do, when they accessed the system, and why. These logs often integrate with ticketing systems like ServiceNow or Jira, providing a clear link between access and business needs. This supports HIPAA's "minimum necessary" standard by ensuring every privileged session is tied to a valid purpose. Gartner has highlighted that mismanagement of identities and privileges is expected to remain a leading cause of cloud security failures [4]. JIT prevents privilege creep, where permissions accumulate unnecessarily over time, by automatically revoking access once a task is completed.
Protecting Patient Data and PHI
JIT works hand-in-hand with Just-Enough Access (JEA) to provide users only the permissions they need for specific tasks. For instance, instead of granting broad "Owner" rights, a user might receive permission solely to "rotate database credentials." Modern JIT systems also incorporate dynamic signals - like device posture, location, or behavior - to identify suspicious activity. If unusual access to PHI is detected, additional multi-factor authentication can be triggered, adding a responsive layer of security that adapts to potential threats in real time.
3. Require Multi-Factor Authentication for Privileged Accounts
Multi-Factor Authentication (MFA) is a powerful safeguard against unauthorized access, even when passwords are compromised [5]. For healthcare cloud environments, implementing MFA for privileged accounts is critical. A single breach of an administrator account could allow attackers to delete cloud configurations or gain access to Protected Health Information (PHI) [2]. MFA works by requiring multiple verification methods - such as a password combined with a biometric scan, hardware token, or time-based code - before granting access to sensitive systems.
This extra layer of security not only protects logins but also reduces exposure to automated attacks.
Reducing Attack Surface
Microsoft reports that enabling MFA can block over 99.9% of automated attacks [3]. This highlights the importance of enforcing MFA not just during login, but also for privilege escalation [5]. By doing so, organizations can prevent attackers from moving laterally within systems after compromising standard accounts.
Healthcare organizations are encouraged to adopt phishing-resistant MFA methods, such as FIDO2 security keys or platform authenticators. Traditional methods like SMS or voice codes are more vulnerable to interception or social engineering attacks and should only be used as a last resort for account recovery, with strict documentation of such exceptions [6].
Meeting HIPAA and Healthcare Compliance Requirements
MFA also plays a key role in meeting HIPAA requirements by bolstering access controls for electronic Protected Health Information (PHI) [6]. Regulatory standards often require MFA as part of administrative and technical safeguards [5]. Each MFA event generates an access log, which can demonstrate compliance to regulators. This layered approach is a cornerstone of HIPAA’s access control mandates, strengthening the overall security framework for healthcare entities.
These practices provide a stronger defense for safeguarding patient data, as outlined below.
Protecting Patient Data and PHI
Healthcare organizations must enforce MFA across all privileged accounts, including those used for EHR systems, remote access, VPNs, and administrative consoles [6]. High-risk vendor accounts should also be protected with MFA, just-in-time access, and session recording. Vendor access should be routed through a Privileged Access Management (PAM) gateway, with session monitoring, restrictions to approved network segments, and access limited to specific maintenance windows. Access should be automatically revoked at the end of a vendor's contract [6].
4. Monitor Privileged Sessions and Record Activity
Keeping a close eye on privileged sessions and recording activities is a critical defense against both external and insider threats. By providing real-time visibility into privileged actions within healthcare cloud systems, session monitoring allows security teams to quickly identify and address suspicious behavior instead of discovering breaches long after the damage is done.
Modern Privileged Access Management (PAM) tools go a step further by recording sessions for forensic investigations. These tamper-proof audit logs serve as solid evidence during compliance audits and aid in incident response efforts. Live monitoring features can also trigger alerts for risky actions - like access attempts from unusual locations or during odd hours - helping to stop potential threats in their tracks. These practices not only bolster security but also simplify compliance with regulatory standards.
Meeting HIPAA and Healthcare Compliance Requirements
From a compliance standpoint, HIPAA requires detailed audit trails and activity logs for any access to electronic Protected Health Information (ePHI) [1]. Session recording fulfills this need by creating tamper-resistant logs that document who accessed patient data, when it happened, and what actions were taken. This level of transparency also helps healthcare organizations align with other security frameworks, such as ISO 27001 and CMMC.
Reducing the Attack Surface
Continuous monitoring plays a key role in minimizing opportunities for attackers. Much like applying least privilege and just-in-time access principles, monitoring reduces the time it takes to detect breaches - from weeks to just minutes. This proactive approach, which can cut incident response times by up to 74% [2], limits lateral movement during an attack and prevents misuse of privileged credentials. It’s a strategy that aligns well with zero-trust security principles, further strengthening the organization’s defenses.
Improving Efficiency in Healthcare Cloud Operations
Behavioral analysis can assign risk scores to sessions, automating threat detection and reducing the need for manual reviews. Using secure workstations with automated threat responses can further enhance efficiency by eliminating the risks associated with standing privileges. Risk-scored sessions and streamlined vendor access not only save time but also improve operational workflows.
Tools like Censinet RiskOps™ provide robust session monitoring and recording features, enabling healthcare organizations to maintain strict control over privileged access while staying compliant with regulatory demands.
5. Review Access Rights Regularly and Manage Vendor Permissions
Access rights aren't static - they evolve as employees change roles, temporary access expires, or new systems are introduced. Yet, privileged accounts often remain active long after they're needed. Regularly reviewing these permissions is crucial. Healthcare organizations should aim for quarterly access reviews, leveraging automated tools to scan privileged accounts. These tools help revoke outdated permissions and ensure access aligns with current roles. For high-risk accounts, such as EHR administrators, peer reviews can add an extra layer of oversight. Integrating this process with ticketing systems for change approvals not only updates privileges but also reduces potential vulnerabilities.
Reducing Attack Surface
Dormant or over-provisioned accounts are like open doors for attackers. Regular access reviews close these gaps by removing unnecessary privileges. In cloud environments, this might include frequent credential rotations and applying zero-trust principles to dynamic resources. For instance, auditing vendor permissions weekly has been shown to cut potential breach risks by up to 50% [9].
Meeting HIPAA and Healthcare Compliance Requirements
HIPAA mandates stringent access controls and proof of least privilege for Protected Health Information (PHI). Periodic access reviews generate essential audit logs, often achieved through quarterly audits, session recordings, and automated deprovisioning tools. These logs not only support compliance with the HIPAA Security Rule §164.312 but also enhance incident response by identifying unauthorized activity. Automated reporting with tamper-resistant logs simplifies preparation for regulatory reviews.
Protecting Patient Data and PHI
By conducting regular access reviews, healthcare organizations can better safeguard patient data. Revoking excessive permissions minimizes the risk of exposing electronic PHI stored in EHRs and cloud systems. Continuous monitoring can also flag unusual access patterns to patient records, reducing the likelihood of breaches and legal consequences. Mismanaged privileged access has been linked to up to 80% of PHI breaches [10]. Combining encryption, session monitoring, and routine access validation helps prevent unauthorized changes to sensitive records.
Improving Efficiency in Healthcare Cloud Operations
Vendor management plays a critical role in healthcare PAM strategies. Treat vendor permissions as high-risk by implementing Business Associate Agreements (BAAs), Role-Based Access Control (RBAC) with Just-In-Time (JIT) access, Multi-Factor Authentication (MFA), and monitored gateways. Set strict timeframes and network segments for vendor access, and automatically terminate permissions when contracts end. Using PAM vaults for short-term credentials tied to change tickets can enhance response times in 24/7 hospital operations while maintaining security. Tools like Censinet RiskOps™ streamline vendor access management with automated workflows and centralized oversight, ensuring both internal and external privileges are tightly controlled.
Conclusion
Healthcare organizations constantly grapple with threats targeting their most sensitive assets - Electronic Health Records (EHRs) and Protected Health Information (PHI). Privileged accounts remain a critical vulnerability, as their misuse can lead to devastating breaches that jeopardize both patient safety and organizational trust in cloud-based systems[7]. By following best practices, healthcare providers can establish a strong security framework that protects vital systems, supports HIPAA compliance, and minimizes the risk of attacks.
Key measures like centralized audit trails, real-time monitoring, strong encryption, and strict third-party risk assessments and vendor access controls significantly reduce vulnerabilities. Adopting these strategies helps organizations achieve tangible improvements, such as reducing standing privileges, identifying suspicious activity faster, and enabling thorough forensic investigations[2][11].
Cloud-based Privileged Access Management (PAM) solutions provide the scalability and adaptability required to manage access across hybrid environments[1]. By incorporating layered security measures aligned with zero trust principles[8], healthcare providers can better defend against the constantly evolving threat landscape.
Start by assessing your current privileged accounts and access controls. Automating processes like provisioning, de-provisioning, and credential rotation reduces human error and ensures consistent security practices[12].
Given the sensitive nature of PHI and patient records, acting promptly is non-negotiable. Implementing these PAM best practices now not only protects your patients but also safeguards your organization's reputation while ensuring compliance with stringent healthcare regulations. For those seeking advanced solutions, Censinet RiskOps™ offers tools specifically designed to address the complexities of today's security challenges. Take the first step by reviewing your current PAM setup to strengthen your healthcare cloud security against emerging threats.
FAQs
How do I start a PAM program in a healthcare cloud environment?
Starting a Privileged Access Management (PAM) program in a healthcare cloud environment requires a structured approach to ensure sensitive data stays protected. Here's how you can begin:
- Audit Privileged Accounts: Start by reviewing all privileged accounts and access permissions. This helps you uncover potential risks and vulnerabilities tied to excessive or unnecessary access.
- Classify by Risk: Categorize accounts based on their risk level. This ensures that high-risk accounts receive stricter controls and monitoring.
- Enforce Role-Based Access Controls (RBAC): Limit access to only what is needed for specific roles. This reduces the chances of unauthorized access to critical systems or data.
- Implement Multi-Factor Authentication (MFA): Add an extra layer of security by requiring multiple forms of verification for privileged accounts.
- Automate Access Management: Use automation for provisioning and deprovisioning access. This ensures that employees gain access quickly when needed and lose it immediately upon role changes or departures.
- Continuous Monitoring: Keep an eye on privileged activities around the clock. This allows you to detect and respond quickly to any unusual or suspicious behavior.
- Perform Regular Audits: Regularly review and update access permissions to maintain a strong security posture and adapt to any changes in the environment.
By following these steps, you can build a solid foundation for managing privileged access in a healthcare cloud environment while addressing potential security challenges effectively.
What’s the easiest way to remove standing privileges using just-in-time access?
The simplest method to eliminate standing privileges is by using just-in-time (JIT) access through a PAM system. This setup provides temporary, time-limited privileged access strictly when it's required. Once the task or session ends, the system automatically revokes the access.
This minimizes risk by ensuring users only hold elevated privileges during approved sessions, avoiding unnecessary or extended access to critical systems.
How should we control and audit vendor privileged access to PHI?
To protect PHI when working with vendors, focus on least privilege access by ensuring users only have access to the information necessary for their role. Implement multi-factor authentication (MFA) to add an extra layer of security, and use continuous monitoring to track activities in real-time. Regular audits of privileged accounts can help identify any unauthorized actions early.
Role-based controls are another key strategy - assign permissions based on specific job functions and limit the scope and duration of access sessions. Keep detailed logs of all activities, as they can be invaluable for investigations if issues arise. Actively monitor vendor sessions to ensure compliance with HIPAA regulations, and immediately revoke access when it’s no longer required. These steps go a long way in reducing potential risks.


