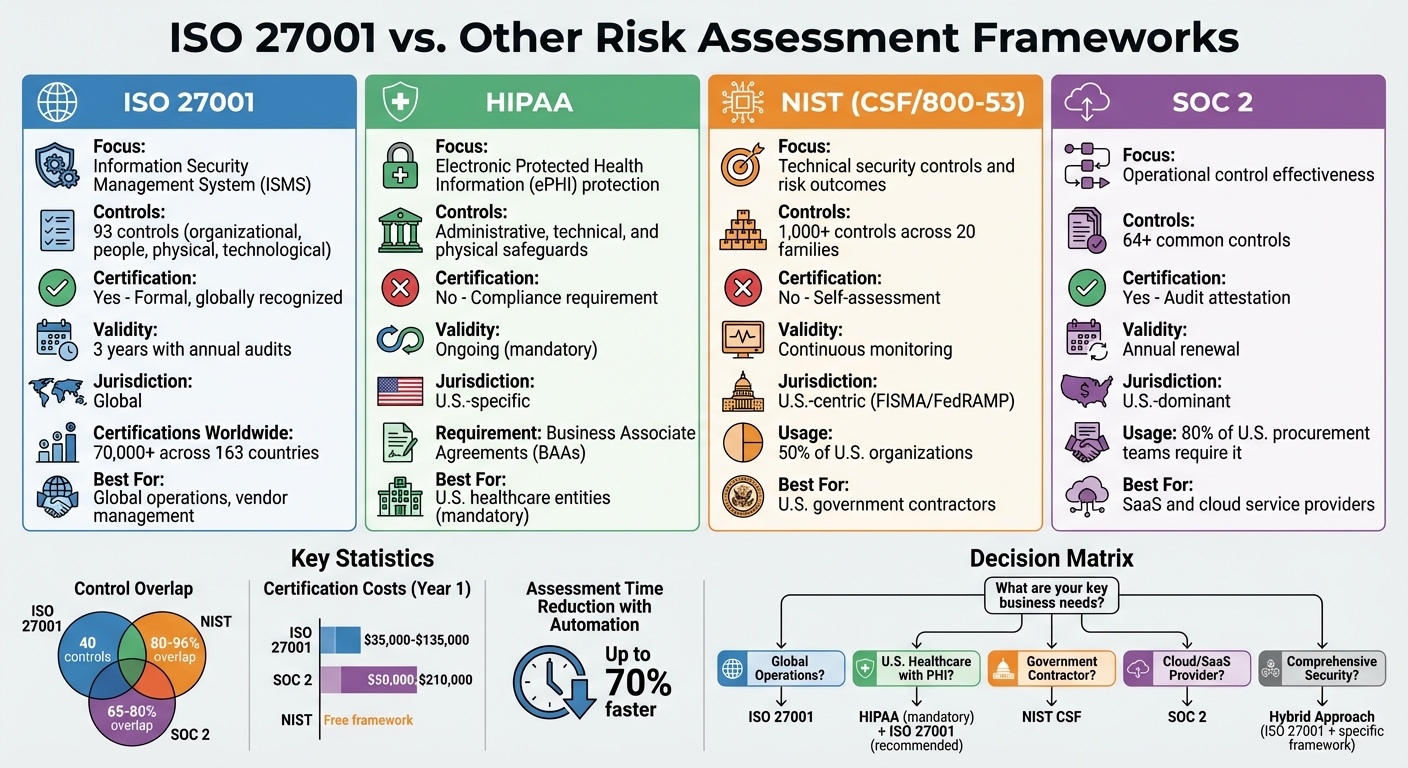
ISO 27001 vs. Other Risk Assessment Frameworks
Post Summary
ISO 27001 is a globally recognized standard for managing information security, offering a structured system to mitigate risks and protect data. For healthcare organizations, it stands out among risk assessment frameworks like HIPAA, NIST, and SOC 2 by providing a formal certification process and comprehensive governance for vendor risk management.
Here’s a quick breakdown of how it compares:
- ISO 27001: Focuses on an Information Security Management System (ISMS), with 93 controls grouped into organizational, people, physical, and technological categories. It offers a formal, globally recognized certification.
- HIPAA: U.S.-specific law for protecting ePHI, requiring Business Associate Agreements (BAAs) but no formal certification.
- NIST: Provides detailed technical controls and maturity tiers but lacks a certification process.
- SOC 2: Focuses on operational effectiveness and Trust Service Criteria, with an audit-based attestation report.
Each framework serves different needs. ISO 27001 is ideal for global operations, while HIPAA is mandatory for U.S. healthcare entities. NIST and SOC 2 cater to technical and operational security, respectively.
Quick Comparison
| Framework | Focus | Certification | Best For |
|---|---|---|---|
| ISO 27001 | ISMS and governance | Yes | Global operations, vendor management |
| HIPAA | ePHI protection | No | U.S. healthcare entities |
| NIST | Technical security controls | No | U.S. government contractors |
| SOC 2 | Operational control effectiveness | Yes | SaaS and cloud service providers |
ISO 27001 can also complement other frameworks, such as HIPAA and SOC 2, to strengthen security and compliance.
ISO 27001 vs HIPAA vs NIST vs SOC 2 Framework Comparison for Healthcare
ISO 27001 vs. HIPAA for Third-Party Risk Assessments
Main Differences Between ISO 27001 and HIPAA
ISO 27001 and HIPAA take very different approaches when it comes to managing third-party risks. Understanding these differences is key for organizations navigating compliance in healthcare or broader industries.
ISO 27001 is a global, voluntary standard designed to establish an Information Security Management System (ISMS). It includes supplier management controls that require documented agreements with vendors and a clear risk treatment plan. On the other hand, HIPAA is a U.S. law that focuses on protecting Electronic Protected Health Information (ePHI). HIPAA’s approach is more prescriptive, requiring Business Associate Agreements (BAAs) to outline how third parties secure ePHI from threats and vulnerabilities.
"ISO 27001 gives you a comprehensive management system; HIPAA defines protections for ePHI." - AccountableHQ [1]
The certification process also highlights their differences. ISO 27001 offers a formal certification valid for three years, with annual surveillance audits to ensure ongoing compliance. Vendors with ISO 27001 certification gain a globally recognized signal of trust. HIPAA, however, doesn’t have an official certification process. Instead, compliance is demonstrated through self-assessments and is enforced by the Office for Civil Rights (OCR) via investigations and penalties. Interestingly, about 40 controls overlap between the two frameworks [3], meaning ISO 27001 can serve as a structural foundation while organizations meet HIPAA's specific legal requirements.
It’s important to note that compliance with one framework doesn’t automatically satisfy the other. The table below provides a side-by-side comparison of their key attributes.
Comparison Table: ISO 27001 vs. HIPAA
| Attribute | ISO 27001 | HIPAA |
|---|---|---|
| Primary Focus | ISMS and continuous improvement | Legal safeguards for the privacy and security of ePHI |
| Risk Assessment Scope | Covers all information assets, systems, and third parties within the ISMS | Focuses on threats and vulnerabilities specific to ePHI |
| Vendor Requirements | Supplier management controls and security clauses in agreements | Requires BAAs to outline ePHI protection |
| Compliance Evidence | Accredited certification, Statement of Applicability (SoA), and audit reports | Security Risk Analysis documentation, policies, and BAA records |
| Monitoring Process | Annual audits and internal management reviews | Periodic evaluations through self-assessments |
| Jurisdiction | Global; applicable across industries | U.S.-specific; applies to healthcare entities and their associates |
sbb-itb-535baee
ISO 27001 vs. NIST Frameworks in Vendor Risk Management
ISO 27001 and NIST: Core Differences
When it comes to managing healthcare vendor risks, ISO 27001 and NIST frameworks take very different approaches. ISO 27001 offers a structured management system that emphasizes the "how" of security governance [8]. It organizes 93 security controls into four categories: organizational, people, physical, and technological [4][8]. On the other hand, NIST SP 800-53 provides a detailed catalog with over 1,000 security and privacy controls spread across 20 families [8]. Essentially, ISO 27001 sets the framework, while NIST dives into the specifics.
"Think of ISO 27001 as a flexible framework that sets the stage for security processes, whereas NIST 800-53 fills in the details with specific controls." - Security Compass [4]
One of the standout differences is certification. ISO 27001 offers a formal three-year certification process with annual audits, which acts as a global "badge" of trust for healthcare vendors [6]. NIST, however, does not provide a certification option. Instead, it relies on self-assessments and maturity tiers (ranging from Tier 1 to Tier 4) [5][6]. While ISO 27001 has over 70,000 certifications worldwide across 163 countries, 50% of U.S. organizations use the NIST Cybersecurity Framework [5].
ISO 27001’s risk-based approach allows organizations to tailor controls to their unique risks [4]. In contrast, NIST 800-53 uses predefined control baselines (Low, Moderate, High) based on data sensitivity [4]. Interestingly, despite these differences, research shows an 80% to 96% overlap between the two frameworks [8]. This has led many healthcare organizations to adopt a hybrid strategy: using ISO 27001 for governance and pairing it with NIST 800-53 for detailed technical implementations [7][8]. These distinctions in strategy and certification heavily influence how organizations manage vendor risks.
Comparison Table: ISO 27001 vs. NIST
| Attribute | ISO 27001 | NIST (CSF / 800-53) |
|---|---|---|
| Primary Focus | Governance and ISMS process [5] | Risk outcomes and technical controls [6] |
| Certification | Third-party accredited; valid three years [4] | No formal certification process [4] |
| Supplier Agreements | Annex A.5.19-A.5.23 requires specific security requirements documented in formal contracts | NIST SP 800-53 "SR" (Supply Chain Risk Management) family provides guidelines for including security in acquisitions |
| Due Diligence | Mandatory risk assessments of suppliers before engagement as part of the ISMS scope | NIST CSF "ID.SC" category focuses on identifying and prioritizing suppliers based on risk impact |
| Vendor Monitoring | Mandatory internal/external audits [7] | Continuous monitoring and maturity tiers [5] |
| Jurisdiction | Global; applicable across industries | U.S.-centric; aligns with FISMA and FedRAMP for federal health data [4] |
| Cost | Standard purchase: $150–$500; Certification audit: $15,000–$50,000 [5][8] | Framework documents are free to download and use [5] |
ISO 27001 vs. SOC 2 vs. HIPAA: Which Compliance Path Suits Your SMB in 2025?
ISO 27001 vs. SOC 2 for Healthcare Vendor Evaluations
Let’s dive deeper into how ISO 27001 and SOC 2 compare when it comes to healthcare vendor evaluations. Each framework brings its own strengths, and understanding their differences can guide organizations in picking the right one.
ISO 27001's Broad Coverage vs. SOC 2's Specific Focus
The main difference between ISO 27001 and SOC 2 lies in their scope and approach. ISO 27001 emphasizes governance through an Information Security Management System (ISMS), which addresses risks across the entire organization. In contrast, SOC 2 zeroes in on operational performance, proving that specific controls work effectively on a day-to-day basis [12]. For healthcare vendors, this distinction is crucial when assessing risk.
ISO 27001 takes a comprehensive approach, covering all information assets within its defined scope and requiring adherence to 93 detailed controls [9][13]. Meanwhile, SOC 2 focuses on safeguarding customer data and aligns with five Trust Service Criteria (TSC): Security, Availability, Processing Integrity, Confidentiality, and Privacy [9][11]. Vendors can tailor SOC 2 to fit their services, making it more flexible, but its narrower focus may not address broader organizational risks.
"ISO 27001 builds institutional accountability, ensuring those controls and the processes behind them continue to mature in the future. One validates execution, the other reinforces endurance." - Drummond Group [12]
Geography also plays a role in framework preference. Globally, ISO 27001 is often considered the standard for international compliance, especially in Europe and Asia [10]. In the U.S., SOC 2 dominates, particularly among SaaS and cloud providers, with over 80% of U.S. procurement teams requiring a SOC 2 report [9]. For global healthcare vendors, ISO 27001 provides a solid foundation for integrating requirements like HIPAA or GDPR [12]. On the other hand, U.S.-based health-tech companies often lean on SOC 2 to demonstrate control effectiveness to domestic partners [12][13].
Differences in Audit and Certification Processes
The audit process for ISO 27001 and SOC 2 varies significantly. ISO 27001 audits are conducted by accredited registrars, resulting in a certificate valid for three years, with annual surveillance audits [9][10]. SOC 2 audits, performed by licensed CPA firms, produce a private attestation report that’s valid for 12 months [9][10]. Among enterprise buyers, 90% prefer SOC 2 Type II reports over Type I, as they reflect operational effectiveness over a 6-12 month period rather than a single point in time [9].
Despite their differences, the two frameworks share a 65% to 80% overlap in controls [9][10]. This overlap has encouraged many healthcare vendors to pursue both certifications. By doing so, they can expand their reach in both U.S. and international markets while reducing redundant work [9][13].
Comparison Table: ISO 27001 vs. SOC 2
| Attribute | ISO 27001 | SOC 2 |
|---|---|---|
| Primary Focus | Governance and Risk Management (ISMS) [12] | Operational Control Effectiveness (TSC) [12] |
| Audit Frequency | 3-year cycle with annual surveillance audits [9][10] | Annual renewal for Type II reports [9][10] |
| Evidence Requirements | Risk register, Statement of Applicability, ISMS policies [11] | Detailed logs, screenshots, and audit trails over 6-12 months [9][11] |
| PHI Handling | Managed via risk assessment and Annex A controls [11] | Specifically addressed if the "Privacy" TSC is included [9][11] |
| Suitability in Healthcare | Best for global vendors and those needing GDPR alignment [9][11] | Best for U.S.-based SaaS and cloud service providers [9][10] |
| Report Type | Publicly recognizable certificate [11] | Private, detailed attestation report for stakeholders [9][11] |
| Cost (Year 1) | $35,000–$135,000 total implementation [9] | $50,000–$210,000 total implementation [9] |
| Number of Controls | 93 (Annex A) [9] | 64+ common controls [9] |
These differences highlight how each framework caters to specific geographic, operational, and compliance needs. Choosing the right one depends on your organization's priorities and the markets you serve.
Using ISO 27001 with Healthcare Risk Management Platforms
Modern platforms like Censinet RiskOps™ demonstrate how ISO 27001 can be effectively implemented in healthcare without relying on outdated spreadsheets or manual processes. These platforms simplify compliance by streamlining the entire process, helping healthcare organizations meet ISO 27001's stringent requirements while managing third-party risks more efficiently.
Simplifying ISO 27001 Compliance with Censinet RiskOps™

Censinet RiskOps™ supports healthcare delivery organizations (HDOs) in achieving ISO 27001 compliance by automating vendor assessments and risk monitoring. The platform includes customizable vendor questionnaires that align with ISO 27001's focus on identifying and managing risks. Tools for continuous monitoring provide real-time risk scoring and alerts on changes in vendor security postures [14][17]. This reduces the manual workload and helps HDOs ensure compliance with controls outlined in ISO 27001 Annex A, such as incident management and supply chain risk mitigation [14][17].
For example, a mid-sized U.S. hospital network used Censinet RiskOps™ to perform ISO 27001-aligned assessments across more than 200 vendors. By automating control mapping, the hospital reduced assessment time by 50%, allowing the team to focus on addressing high-risk PHI exposures in their supply chain rather than drowning in paperwork. The platform also includes pre-built assessments for areas like PHI protection and medical device security. This enables HDOs to benchmark vendors against healthcare regulations while managing ISO-aligned risks, particularly those tied to supply chain vulnerabilities [16]. This level of automation not only saves time but also enhances collaboration, as discussed further in the next section.
Benefits of Automation and Collaboration
Automation plays a key role in driving efficiency, and Censinet RiskOps™ excels at applying automation to ISO 27001 compliance. Features like AI-powered risk scoring and workflow orchestration reduce the manual effort required for implementing risk treatment plans, enabling healthcare organizations to focus on critical areas like PHI and medical device security [14][15]. Automated processes allow assessments to run up to 70% faster compared to traditional manual methods. This scalability is essential for managing growing vendor networks while adhering to ISO 27001's principle of continual improvement [14][15].
Censinet's AITM (Artificial Intelligence for Third-Party Management) further accelerates risk assessments by enabling vendors to quickly complete security questionnaires. The platform automatically summarizes vendor evidence, captures key integration details, identifies fourth-party risks, and generates risk summary reports. Importantly, a human-in-the-loop approach ensures that automation supports rather than replaces critical decision-making. Risk teams maintain control through configurable rules and review processes, striking a balance that allows healthcare leaders to scale operations effectively. This approach not only aligns with ISO 27001's governance standards but also ensures patient safety and uninterrupted care delivery.
Choosing the Right Framework for Healthcare Third-Party Risks
Main Takeaways from the Comparisons
ISO 27001 provides a risk-based framework for managing information security, featuring 93 controls and a formal certification valid for three years [2]. It offers strong governance for healthcare organizations, especially those operating internationally or managing complex vendor networks. However, using ISO 27001 by itself doesn't guarantee compliance with U.S. legal standards for protecting patient data.
HIPAA is a mandatory requirement for any U.S. entity handling Protected Health Information (PHI). It focuses on administrative, technical, and physical safeguards [2]. As OneTrust explains, "HIPAA and ISO 27001 are complementary frameworks that together strengthen security" [2]. ISO 27001 can provide the structure needed to implement HIPAA requirements effectively.
NIST CSF focuses on five core functions - Identify, Protect, Detect, Respond, and Recover - making it an excellent choice for organizations aiming for detailed technical security improvements aligned with U.S. government standards [19]. On the other hand, SOC 2 centers around the Trust Services Criteria and includes continuous evidence mapping, which is particularly useful for assessing cloud-based or SaaS healthcare vendors [18][19]. While NIST CSF lacks a formal certification process, SOC 2 relies on audit attestations to demonstrate compliance.
Decision Criteria for Framework Selection
Based on these comparisons, here are some key factors to consider when choosing the right framework. Healthcare organizations managing PHI must prioritize HIPAA compliance to avoid federal penalties. Using ISO 27001 as a management system can help implement HIPAA requirements more effectively [2][19]. For organizations with global operations, ISO 27001's international recognition is advantageous. Meanwhile, those focusing solely on U.S. markets might find NIST CSF or SOC 2 better suited to domestic standards.
| Framework | Primary Strength | Certification Available | Ideal Use Case |
|---|---|---|---|
| ISO 27001 | Global governance and structured ISMS | Yes (3-year validity) | International operations and comprehensive security management |
| HIPAA | Legal protection for PHI | No (compliance requirement) | Mandatory for U.S. entities handling patient data |
| NIST CSF | Tactical security controls | No (voluntary framework) | Government contractors and critical infrastructure |
| SOC 2 | Trust Services criteria with attestation-based validation | Yes (audit attestation) | Cloud service providers and SaaS vendors |
When evaluating cloud vendors, asking for SOC 2 reports can help confirm adherence to the Trust Services Criteria [18][19]. For third parties handling PHI, ensuring HIPAA compliance is critical. Utilizing common healthcare third-party risk assessment questions can help verify this compliance during the vetting process. Once HIPAA requirements are met, ISO 27001 controls can be layered on to address broader security risks. Many U.S. healthcare organizations streamline compliance by mapping ISO 27001 controls to HIPAA and SOC 2 requirements [19]. Tools like Censinet RiskOps™ support this integrated approach, making it easier to manage multiple frameworks efficiently.
FAQs
If we’re HIPAA compliant, do we still need ISO 27001?
Even with HIPAA compliance in place, adopting ISO 27001 can add significant value. While HIPAA is specifically designed to safeguard Protected Health Information (PHI) within the U.S., ISO 27001 offers a more comprehensive framework that addresses organization-wide information security risks.
ISO 27001 strengthens security efforts by incorporating structured risk assessments, ongoing improvements, and the option for certification. Unlike HIPAA, it covers all information assets, not just PHI. Combining both standards creates a more robust approach to security and regulatory compliance.
What ISO 27001 evidence should we ask vendors for?
When evaluating a vendor's ISO 27001 compliance, it's important to focus on specific documentation that confirms their adherence to the standard. Here's what to look for:
- ISO 27001 certification or audit reports: These confirm that the vendor has undergone an independent assessment of their compliance with the standard.
- Risk management and assessment reports: These documents detail how the vendor identifies, evaluates, and mitigates risks to their information security.
- Security policies and procedures: These should align with ISO 27001 controls and demonstrate the vendor's commitment to maintaining secure practices.
- Evidence of ongoing improvement: Look for records of internal audits, corrective actions, or other measures that show the vendor is actively refining their security processes.
By reviewing these materials, you can gain a clearer picture of how well the vendor adheres to ISO 27001 requirements.
How do we map ISO 27001 to NIST and SOC 2 without duplicating work?
Mapping ISO 27001 to NIST and SOC 2 can feel like a complex task, but with the right approach, it becomes much more manageable. Start by taking a detailed inventory of your ISO 27001 controls. Then, map these controls to their counterparts in both the NIST Cybersecurity Framework (CSF) and SOC 2. By identifying areas of overlap, you can streamline your efforts and avoid wasting time on redundant processes.
Using tools like crosswalk matrices can make this process smoother and more accurate. These tools help you clearly see how controls align across frameworks. At the same time, keeping thorough documentation is essential. It not only supports a unified compliance strategy but also helps reduce duplication and strengthens your overall security program.


