GDPR vs. HIPAA: Key Differences in Incident Response
Post Summary
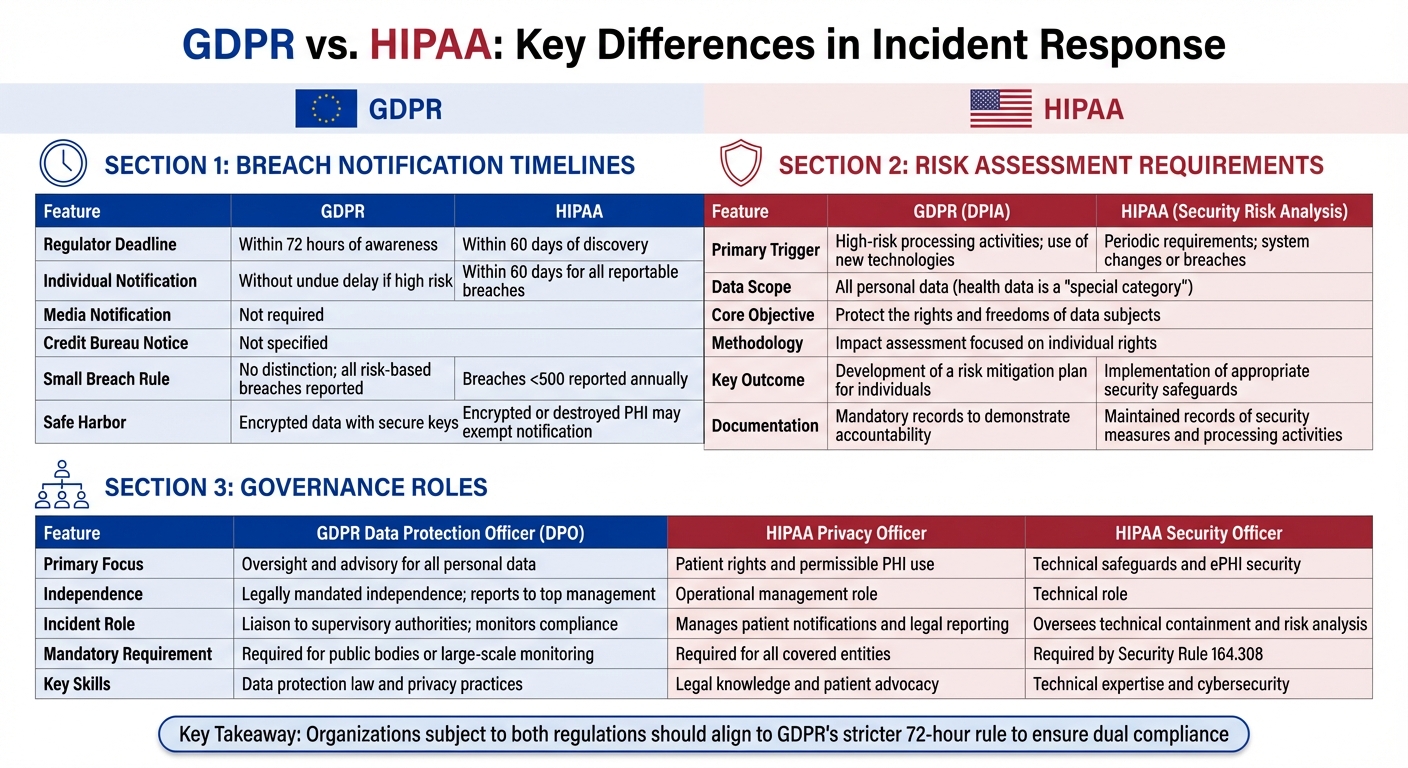
GDPR requires notifying the appropriate supervisory authority within 72 hours of confirming a breach and notifying affected individuals without undue delay when high risk to their rights and freedoms exists. HIPAA allows up to 60 days from discovery to notify affected individuals and HHS, with additional media notification required for breaches affecting 500 or more individuals in a single state and credit bureau notification for breaches affecting 1,000 or more. GDPR's risk assessment focuses on individual rights through Data Protection Impact Assessments; HIPAA's Security Risk Analysis focuses on system vulnerabilities and safeguards. GDPR requires an independent Data Protection Officer; HIPAA requires Privacy and Security Officers in operational management roles.
GDPR's 72-hour supervisory authority notification begins when there is reasonable certainty a breach has occurred. HIPAA's 60-day window begins at the date of discovery — defined as when the breach is known or should reasonably have been known. For organizations subject to both frameworks, adopting GDPR's 72-hour rule as the default timeline for all incidents ensures simultaneous compliance with both frameworks without maintaining separate workflows. GDPR permits phased notifications — organizations can submit initial reports within 72 hours and follow up as investigations progress — providing flexibility that aligns with HIPAA's requirement for thorough analysis. Both frameworks include safe harbors for encrypted data.
GDPR's Data Protection Impact Assessment is required whenever processing activities present high risks to individuals' rights and freedoms. Because health data is classified as a special category under GDPR, its processing nearly always requires a DPIA. The DPIA outlines risks to individual rights, explains the nature of processing, and proposes mitigation strategies — with mandatory documentation demonstrating accountability under GDPR Article 5. HIPAA's Security Risk Analysis focuses on identifying and addressing potential risks to the confidentiality, integrity, and availability of ePHI through technical, administrative, and physical safeguards. HIPAA's analysis is triggered periodically and by system changes; GDPR's DPIA is triggered by high-risk processing activities. A single harmonized risk assessment framework can address the requirements of both.
GDPR requires a Data Protection Officer who operates independently, reports directly to top management, and is protected from job-related risks during their duties. During a breach, the DPO coordinates with Data Protection Authorities, ensures GDPR's 72-hour notification deadline is met, and serves as the individual rights liaison. HIPAA requires two operational roles: the Privacy Officer responsible for patient rights, PHI use compliance, and notification requirements, and the Security Officer under Security Rule 164.308 responsible for technical containment, forensic investigation, and ePHI protection. Organizations with 500 or more employees should maintain these as distinct roles due to their different skill requirements — legal expertise for Privacy Officers and technical cybersecurity expertise for Security Officers.
The practical foundation is adopting GDPR's 72-hour notification window as the default timeline for all incidents, eliminating the need for separate workflows while ensuring compliance with both frameworks. A multidisciplinary response team including IT, clinical, legal, and compliance experts should be activated within the first hour of any incident, with pre-drafted notification templates prepared for both EU supervisory authorities and HHS. GDPR's DPO and HIPAA's Privacy and Security Officers must coordinate to ensure notifications are consistent across jurisdictions. Forensic and risk assessment reports should be routed through legal counsel to maintain attorney-client privilege. State-specific deadlines such as New York's SHIELD Act requiring reporting within 30 days must be tracked alongside federal obligations.
Censinet RiskOps™ automates detection, documentation, and reporting workflows that manual processes cannot sustain — particularly critical given that manual errors account for approximately 74% of data breach incidents. The platform provides automated data discovery and inventory tools that distinguish between PHI and GDPR special category health data in advance of incidents, preventing last-minute classification delays. When a breach occurs, Censinet RiskOps™ streamlines risk assessment by quantifying potential individual harm, provides a centralized command center with visibility across the organization's risk landscape, and maintains the comprehensive audit trails that both EU and U.S. regulators require. Pre-drafted notification templates integrate with case management features to reduce response times within the critical 72-hour GDPR window.
GDPR and HIPAA are two major data protection regulations that govern how organizations handle sensitive information. While GDPR applies globally to data involving EU residents, HIPAA focuses on safeguarding health information within the U.S. Here’s a quick summary of their key differences:
For organizations subject to both regulations, aligning processes to GDPR’s stricter 72-hour rule and maintaining clear governance roles can simplify compliance and reduce risks.
GDPR vs HIPAA Incident Response Requirements Comparison Chart
GDPR and HIPAA Compliance Secrets You Need to Know
sbb-itb-535baee
Breach Notification Timelines
When a data breach happens, the response clock starts ticking - but the deadline to act depends on the specific regulation. GDPR and HIPAA each have their own timelines, and understanding these differences is key to avoiding fines and maintaining credibility. This is especially critical as cyberattacks and data breaches continue to disrupt clinical applications and patient care. Here's how each regulation shapes the response process.
GDPR's 72-Hour Notification Rule
Under GDPR, organizations must notify the appropriate supervisory authority within 72 hours of confirming a breach. This countdown begins when there's reasonable certainty that a breach has occurred. If the breach is likely to create a high risk to individuals' rights and freedoms, affected individuals must also be informed without undue delay.
Miss the 72-hour window? You'll need to provide a detailed justification to the supervisory authority. However, if the compromised data was encrypted with a strong, uncompromised key, the breach may not require notification since the risk is considered minimal.
HIPAA's 60-Day Notification Requirements
HIPAA gives organizations 60 days from the discovery of a breach to notify affected individuals and the Department of Health and Human Services (HHS). Discovery is defined as the date the breach is known - or should reasonably have been known.
For breaches impacting 500 or more individuals in a single state or jurisdiction, notification must also be sent to prominent media outlets. If 1,000 or more individuals are affected, the three major credit reporting agencies (Equifax, Experian, and TransUnion) must be informed. Smaller breaches, involving fewer than 500 individuals, are reported to HHS annually in a consolidated log.
HIPAA also includes a safe harbor provision: if a formal risk assessment determines there's a low probability that protected health information (PHI) was compromised, notification may not be necessary. This often applies when data is encrypted or destroyed.
Comparison Table: Notification Timelines and Requirements
Feature
GDPR
HIPAA
Regulator Deadline
Within 72 hours of awareness
Within 60 days of discovery
Individual Notification
Without undue delay if high risk
Within 60 days for all reportable breaches
Media Notification
Not required
Required if 500+ individuals affected
Credit Bureau Notice
Not specified
Required if 1,000+ individuals affected
Small Breach Rule
No distinction; all risk-based breaches reported
Breaches <500 reported annually
Safe Harbor
Encrypted data with secure keys
Encrypted or destroyed PHI may exempt notification
For organizations governed by both GDPR and HIPAA, following GDPR's 72-hour rule ensures compliance with HIPAA's 60-day requirement. To meet these demands, organizations may need tools like real-time log monitoring, automated anomaly detection, and a preliminary breach assessment completed within 48 hours. This approach not only supports compliance but also strengthens overall incident response efforts, especially for healthcare providers navigating these dual regulations.
Risk Assessment Requirements
Risk assessments play a critical role in identifying vulnerabilities and safeguarding sensitive data. However, the approaches of GDPR and HIPAA differ significantly when it comes to triggers, methods, and intended outcomes.
Data Protection Impact Assessments (DPIAs) Under GDPR
Under GDPR, a Data Protection Impact Assessment (DPIA) is required whenever processing activities present high risks to individuals' rights. Since health data is classified as a "special category" under GDPR, its processing nearly always necessitates a DPIA [1].
"GDPR requires Data Protection Impact Assessments (DPIAs) for processing that poses high risk to individuals. Health data processing almost always qualifies."
– Aleksander Cudny, Business Analyst,
A DPIA outlines potential risks, explains the nature of the processing, and suggests mitigation strategies. GDPR’s accountability principle (Article 5[1]) further mandates that organizations document these assessments to demonstrate compliance. Ignoring this requirement can lead to severe penalties - up to 4% of annual global turnover or €20 million, whichever is higher [1].
While GDPR centers on protecting individual rights through DPIAs, HIPAA takes a different path by focusing on system vulnerabilities.
Security Risk Analysis Under HIPAA
HIPAA emphasizes ongoing, periodic assessments to identify and address potential risks to the confidentiality, integrity, and availability of electronic Protected Health Information (ePHI) [1]. These assessments are often triggered by changes such as new technology implementations, system upgrades, or potential security incidents.
Unlike GDPR's focus on individual rights, HIPAA's Security Risk Analysis prioritizes implementing technical, administrative, and physical safeguards to prevent unauthorized access and data loss. The regulation requires "reasonable" safeguards, tailored to the size and complexity of the entity [5]. Penalties under HIPAA vary, ranging from $100 to $50,000 per violation, with an annual cap of $1.5 million for repeated violations [1].
Comparison Table: Risk Assessment Triggers and Processes
Feature
GDPR (DPIA)
HIPAA (Security Risk Analysis)
Primary Trigger
High-risk processing activities; use of new technologies
Periodic requirements; system changes or breaches
Data Scope
All personal data (health data is a "special category")
Protected Health Information (PHI)
Core Objective
Protect the rights and freedoms of data subjects
Ensure the confidentiality, integrity, and availability of PHI
Methodology
Impact assessment focused on individual rights
Vulnerability and threat analysis of systems , including those posed by
Key Outcome
Development of a risk mitigation plan for individuals
Implementation of appropriate security safeguards
Documentation
Mandatory records to demonstrate accountability
Maintained records of security measures and processing activities
Bridging the Gap Between GDPR and HIPAA
The differences between GDPR and HIPAA highlight the need for a unified approach to risk assessments, especially for organizations subject to both regulations. A harmonized framework can simplify compliance by addressing the requirements of both standards. Aleksander Cudny reflects on this advantage:
"Both [GDPR and HIPAA risk assessments] can be addressed through a single risk assessment framework that covers the requirements of each regulation"
.
To streamline compliance, organizations should tag data records with their applicable regulatory jurisdiction at the point of collection. This ensures that the correct risk assessment processes and data lifecycle rules are applied automatically. Since GDPR's requirements are often broader, using GDPR as a baseline can help cover much of what HIPAA demands.
Roles and Governance Structures in Incident Response
When it comes to managing incident response effectively, setting up well-defined governance roles is a must. Both GDPR and HIPAA approach this differently. GDPR emphasizes independent oversight, while HIPAA focuses on operational roles to handle daily compliance tasks.
Data Protection Officer (DPO) Under GDPR
The Data Protection Officer (DPO) plays a pivotal role in GDPR compliance, acting as an independent advisor for all personal data processing activities. Healthcare organizations that process health data, classified as a "special category" under GDPR, are legally required to appoint a DPO [2].
What sets the DPO apart is their independence. They report directly to top management and are protected from job-related risks while performing their duties [6][7]. In the event of a breach, the DPO coordinates with Data Protection Authorities, ensures compliance with GDPR’s 72-hour notification deadline, and serves as a go-to resource for individuals exercising their data rights [4][6][8]. If there’s a delay in notification, the DPO must document the reasons, as the organization bears the burden of proof [4].
"The DPO operates independently, avoids conflicts of interest, and reports to the highest management level."
– Kevin Henry, HIPAA Expert
Unlike operational roles, the DPO doesn’t handle technical or forensic aspects of a breach. Their focus is on ensuring the response aligns with GDPR's accountability principles [6][8]. For smaller healthcare organizations, hiring an external consultant as a DPO can be a cost-efficient alternative to employing one full-time [2].
Privacy and Security Officers Under HIPAA
HIPAA takes a different route by requiring two key operational roles: the Privacy Officer and the Security Officer [8]. These roles are hands-on, managing compliance policies and technical safeguards on a daily basis, unlike the advisory nature of a GDPR DPO [6][8].
The Privacy Officer is responsible for patient rights and ensuring that Protected Health Information (PHI) is used appropriately. During an incident, they handle notification requirements and patient communication [8]. On the other hand, the Security Officer, as mandated by Security Rule 164.308, focuses on technical containment, forensic investigations, and protecting electronic PHI (ePHI) [9][10].
"Privacy is related to the disclosure of patient data, whereas security is focused on the actual IT protocols (e.g. passwords and encryption) put in place to safeguard that data."
–
Organizations with 500 or more employees should consider keeping these roles separate due to their distinct skill requirements. The Privacy Officer needs expertise in legal matters and patient advocacy, while the Security Officer requires strong technical and cybersecurity knowledge [8][9].
Comparison Table: Governance Roles and Responsibilities
Feature
GDPR Data Protection Officer (DPO)
HIPAA Privacy Officer
HIPAA Security Officer
Oversight and advisory for all personal data
Patient rights and permissible PHI use
Technical safeguards and ePHI security
Legally mandated independence; reports to top management
Operational management role
Technical role
Liaison to supervisory authorities; monitors compliance
Manages patient notifications and legal reporting
Oversees technical containment and risk analysis
Required for public bodies or large-scale monitoring
Required for all covered entities
Required by Security Rule 164.308
Data protection law and privacy practices
Legal knowledge and patient advocacy
Technical expertise and cybersecurity
Having clearly defined roles under both GDPR and HIPAA strengthens incident response processes. This alignment is a key finding in recent healthcare cybersecurity benchmarking studies that track industry maturity. GDPR’s 72-hour rule can help streamline internal procedures, while HIPAA’s focus on operational roles ensures no aspect of compliance is overlooked. Additionally, organizations should prepare a documented succession plan for the HIPAA Security Officer to avoid lapses in compliance if the position becomes vacant unexpectedly [8].
Building a Unified Incident Response Strategy
Healthcare organizations in the U.S. and EU face the challenge of navigating two distinct regulatory frameworks: GDPR's 72-hour breach notification deadline and HIPAA's more lenient 60-day window. Instead of juggling separate processes, organizations can streamline their efforts by creating a unified incident response strategy. This approach not only reduces administrative complexity but also ensures compliance with both standards.
Using GDPR's 72-Hour Deadline as a Baseline
A practical starting point is adopting GDPR's stricter 72-hour notification window as the default timeline for all incidents[12]. This approach ensures compliance with both GDPR and HIPAA while eliminating the need for separate workflows. The breach clock starts immediately, fostering a culture of urgency.
GDPR allows phased notifications, meaning if full details aren’t available within 72 hours, organizations can submit initial reports and follow up as investigations progress[12]. This flexibility aligns with HIPAA’s requirements for thorough analysis. To maintain momentum, activate a response team within the first hour of an incident. Assign roles promptly and use pre-drafted notification templates tailored for EU supervisory authorities and the U.S. Department of Health and Human Services (HHS)[4][12]. This preparation ensures rapid response when every minute counts.
Integrating HIPAA-Specific Reporting Requirements
While GDPR sets the timeline, HIPAA brings specific reporting triggers that must be incorporated into the unified strategy. For example, GDPR requires reporting when individual rights and freedoms are at risk[12], while HIPAA focuses on breaches involving unauthorized access, use, or disclosure of Protected Health Information (PHI)[10]. These nuances should guide the notification process.
To handle these requirements effectively, form multidisciplinary teams that include IT, clinical, legal, and compliance experts[11]. Coordination between GDPR Data Protection Officers and HIPAA Privacy and Security Officers is essential to ensure notifications are consistent across jurisdictions[11][2]. Additionally, routing forensic and risk assessment reports through legal counsel can help maintain attorney-client privilege during regulatory inquiries or litigation[4]. Don’t forget to track state-specific deadlines - like New York’s SHIELD Act, which requires reporting within 30 days - to ensure no secondary obligations are overlooked[4].
How Censinet RiskOps™ Supports Incident Response
Technology can play a critical role in simplifying this dual compliance challenge. Manual processes are prone to errors, which are a leading cause of data breaches, accounting for about 74% of incidents[2]. Platforms like Censinet RiskOps™ automate detection, documentation, and reporting workflows, enabling healthcare organizations to meet GDPR and HIPAA requirements more efficiently.
Censinet RiskOps™ offers automated data discovery and inventory tools that help distinguish between PHI and special category health data ahead of time, avoiding last-minute classification issues during incidents[11][2]. When a breach occurs, the platform streamlines risk assessment by quantifying the potential harm to individuals[4]. Its centralized command center provides visibility across the organization’s risk landscape, allowing teams to respond cohesively while maintaining the comprehensive audit trails regulators expect. Pre-drafted templates integrate seamlessly with the platform’s case management features, further reducing response times.
"It's far cheaper and more efficient to embed your data protection bits at the beginning than create your shiny new thing and think, 'where are we going to put that data protection bit now?'" – Kristy Gouldsmith, Data Protection, Privacy, and Cybersecurity Partner, Spencer West LLP
With healthcare data breaches averaging $11.05 million per incident in 2024 - the highest of any industry - investing in tools like Censinet RiskOps™ is not just practical but financially crucial[4]. These technologies help organizations minimize risk exposure while demonstrating accountability to both EU and U.S. regulators through consistent documentation and notification practices.
Conclusion
Key Differences Between GDPR and HIPAA
One of the most striking differences between GDPR and HIPAA lies in their notification timelines. GDPR requires organizations to report breaches to Data Protection Authorities within 72 hours of discovery. In contrast, HIPAA allows up to 60 days to notify both individuals and the HHS when a breach impacts 500 or more people[4]. These differing deadlines push healthcare organizations to establish efficient response protocols tailored to each regulation.
Another notable difference is in their risk assessment criteria. Under GDPR, individual notifications are necessary only if there's a "high risk" to the rights and freedoms of individuals. HIPAA, on the other hand, uses a "harm-based safe harbor", allowing organizations to forgo notification if a written risk assessment determines there's a low probability that PHI was compromised[4]. Understanding these frameworks is crucial for avoiding unnecessary alerts while staying compliant.
Lastly, their governance structures vary. GDPR requires certain organizations to appoint a Data Protection Officer, while HIPAA mandates separate Privacy and Security Officers. This creates distinct yet overlapping areas of accountability that organizations must carefully manage.
These differences underscore the importance of efficient tools and strategies to navigate compliance with both regulations.
How Technology Simplifies Dual Compliance
Given the complexity of managing GDPR and HIPAA requirements simultaneously, relying on manual processes can lead to costly mistakes. With GDPR fines reaching up to €20 million or 4% of global annual revenue[4], the financial risks are enormous. This is where technology, like Censinet RiskOps™, becomes indispensable.
Censinet RiskOps™ automates critical processes such as detection, documentation, and reporting, ensuring compliance with GDPR's 72-hour deadline and HIPAA's specific requirements. By centralizing data management, the platform eliminates the need for separate systems and reduces the risk of human error. For instance, it automatically identifies and classifies PHI and EU resident data, removing the chaos of last-minute breach responses.
The platform also provides a centralized dashboard for real-time tracking and pre-drafted templates to speed up incident responses. Detailed audit trails and automated workflows ensure that healthcare organizations can demonstrate compliance to both European regulators and the U.S. Department of Health and Human Services. By streamlining breach responses and maintaining meticulous records, Censinet RiskOps™ turns the challenge of dual compliance into an operational strength.
FAQs
When does the GDPR 72-hour breach clock start?
When the data controller becomes aware of a personal data breach that may affect individuals' rights and freedoms, the 72-hour GDPR breach notification clock starts ticking. "Awareness" in this context generally means having a reasonable level of certainty that a breach has occurred and that it involves personal data.
If we follow GDPR’s 72-hour rule, will we still meet HIPAA requirements?
Adhering to GDPR's 72-hour breach notification rule can be a helpful way to stay ahead of HIPAA's more relaxed 60-day notification requirement. However, it's not just about meeting the timeline. HIPAA has its own set of rules for how breaches must be documented and reported. While following GDPR's stricter timeline might put you in a good position, you still need to carefully address all of HIPAA's specific obligations to ensure you're fully compliant.
How should we handle a breach that involves both PHI and EU personal data?
When dealing with breaches that involve both Protected Health Information (PHI) and EU personal data, it's crucial to adhere to the strictest standards set by GDPR and HIPAA. Here's how each regulation approaches breach notifications:
To ensure compliance with both frameworks, conducting thorough risk assessments and issuing timely notifications are non-negotiable. Tools like Censinet RiskOps™ can help streamline compliance efforts and manage these processes effectively.
Related Blog Posts
- GDPR vs HIPAA: Cloud PHI Compliance Differences
- GDPR vs. HIPAA: Key Differences for Healthcare
- GDPR vs. HIPAA: Cross-Border Breach Rules
- GDPR Risk Assessment vs. HIPAA Compliance
{"@context":"https://schema.org","@type":"FAQPage","mainEntity":[{"@type":"Question","name":"When does the GDPR 72-hour breach clock start?","acceptedAnswer":{"@type":"Answer","text":"<p>When the data controller becomes aware of a personal data breach that may affect individuals' rights and freedoms, the <strong>72-hour GDPR breach notification clock</strong> starts ticking. "Awareness" in this context generally means having a reasonable level of certainty that a breach has occurred and that it involves personal data.</p>"}},{"@type":"Question","name":"If we follow GDPR’s 72-hour rule, will we still meet HIPAA requirements?","acceptedAnswer":{"@type":"Answer","text":"<p>Adhering to <strong>GDPR's 72-hour breach notification rule</strong> can be a helpful way to stay ahead of HIPAA's more relaxed <strong>60-day notification requirement</strong>. However, it's not just about meeting the timeline. HIPAA has its own set of rules for how breaches must be documented and reported. While following GDPR's stricter timeline might put you in a good position, you still need to carefully address all of HIPAA's specific obligations to ensure you're fully compliant.</p>"}},{"@type":"Question","name":"How should we handle a breach that involves both PHI and EU personal data?","acceptedAnswer":{"@type":"Answer","text":"<p>When dealing with breaches that involve both Protected Health Information (PHI) and EU personal data, it's crucial to adhere to the strictest standards set by <strong>GDPR</strong> and <strong>HIPAA</strong>. Here's how each regulation approaches breach notifications:</p> <ul> <li> <strong>GDPR</strong>: Requires notification within <strong>72 hours</strong> of discovering a breach. The focus here is on maintaining transparency with EU residents and notifying relevant authorities promptly. </li> <li> <strong>HIPAA</strong>: Mandates reporting breaches of electronic PHI (ePHI) within <strong>60 days</strong>. The emphasis lies on risk mitigation and ensuring affected individuals, as well as the Department of Health and Human Services (HHS), are informed. </li> </ul> <p>To ensure compliance with both frameworks, conducting thorough risk assessments and issuing timely notifications are non-negotiable. Tools like <strong>Censinet RiskOps™</strong> can help streamline compliance efforts and manage these processes effectively.</p>"}}]}
Key Points:
Why do GDPR and HIPAA create dual compliance challenges for healthcare organizations in incident response and what are the financial stakes?
- Healthcare breach costs at $11.05 million per incident in 2024 — highest of any industry — The financial consequence of inadequate incident response in healthcare is the highest in any sector, establishing GDPR and HIPAA dual compliance not as an administrative burden but as a direct financial protection mechanism for organizations whose breach costs dwarf those in comparable industries.
- 74% of data breaches caused by manual errors — The near-three-quarters majority of data breach incidents attributable to manual process failures establishes automated incident response infrastructure as a patient safety and compliance necessity rather than an efficiency preference. Manual breach identification, classification, and notification processes fail at rates that make dual compliance structurally unachievable without automation.
- Conflicting timelines requiring simultaneous management — GDPR's 72-hour supervisory authority notification and HIPAA's 60-day individual and HHS notification are not merely different — they are concurrent obligations triggered by the same incident. Organizations that manage them as sequential activities rather than parallel obligations will fail one framework while complying with the other.
- GDPR's global reach versus HIPAA's U.S. sector specificity — GDPR applies globally to processing activities involving EU residents regardless of where the processing organization is located, while HIPAA applies to U.S. covered entities and business associates handling PHI regardless of the nationality of the patients involved. Healthcare organizations with EU patients or EU-based operations face both frameworks simultaneously and cannot assume that compliance with one satisfies the other.
- GDPR fines up to €20 million or 4% of global annual turnover — GDPR's maximum penalty of €20 million or 4% of global annual turnover for the most serious violations — including inadequate breach notification — applies on top of HIPAA penalties ranging from $100 to $50,000 per violation with an annual cap of $1.5 million. Dual compliance failure creates exposure under both penalty structures simultaneously.
- Healthcare data as GDPR special category requiring heightened protection — Under GDPR, health data is classified as a special category of personal data subject to the most stringent processing requirements — including the near-universal DPIA requirement for health data processing. This special category classification means that virtually all healthcare data processing activities require the most rigorous GDPR compliance measures, not the general-purpose protections that apply to standard personal data.
How do GDPR's 72-hour notification requirement and HIPAA's 60-day window differ in their triggers, scope, and phased notification allowances?
- GDPR's clock starts at reasonable certainty, not confirmed completion — GDPR's 72-hour notification window begins when there is reasonable certainty that a breach has occurred — not when a full investigation has been completed or all affected individuals have been identified. Organizations that wait for investigation completion before notifying the supervisory authority risk missing the deadline even when they believe notification cannot be adequately detailed within 72 hours.
- HIPAA's 60-day clock starts at discovery — HIPAA's notification window begins at discovery — the date the breach is known or should reasonably have been known — not at the date of confirmed breach determination. The "should have been known" standard means that a breach discovered during a security audit triggers the 60-day clock even if the organization did not actively identify the breach through its monitoring systems.
- GDPR phased notification enabling compliance under investigation pressure — GDPR explicitly permits phased notifications where initial reports are submitted within 72 hours with the information available at that time, followed by supplemental reports as investigation findings develop. This phased approach enables compliance with the 72-hour deadline even when full breach scope is not yet determined — a flexibility that organizations must utilize proactively rather than assuming they can delay until investigations are complete.
- HIPAA media and credit bureau notifications with no GDPR equivalents — HIPAA's requirement to notify prominent media outlets for breaches affecting 500 or more individuals in a single state and credit reporting agencies for breaches affecting 1,000 or more individuals has no direct GDPR equivalent. These HIPAA-specific obligations must be tracked separately in dual compliance programs and may require coordination with communications and legal teams on timelines that are not addressed in GDPR notification workflows.
- Safe harbors under both frameworks for encrypted data — Both frameworks provide safe harbor protections for encrypted data. GDPR allows organizations to forego notification if compromised data was encrypted with a strong, uncompromised key since the risk to individuals is considered minimal. HIPAA provides safe harbor when a risk assessment determines there is a low probability that PHI was compromised — often applicable when data was encrypted or destroyed. Organizations should document encryption status as a standard incident response step to enable safe harbor determinations.
- Adopting GDPR's 72-hour window as the universal baseline — For organizations subject to both frameworks, adopting GDPR's 72-hour window as the default for all incidents — not only those involving EU residents — eliminates the need for parallel notification workflows and ensures that HIPAA's 60-day deadline is always satisfied as a consequence of GDPR compliance. This baseline approach also builds the organizational response culture that GDPR's 72-hour requirement demands.
How do GDPR's Data Protection Impact Assessments and HIPAA's Security Risk Analysis differ in purpose, triggers, and outcomes?
- DPIA's focus on individual rights versus Security Risk Analysis focus on system vulnerabilities — The fundamental philosophical difference between GDPR's DPIA and HIPAA's Security Risk Analysis is the object of protection. DPIAs assess risks to individuals' rights and freedoms — asking whether processing could cause discrimination, identity theft, financial loss, or reputational damage to affected persons. Security Risk Analysis assesses risks to system confidentiality, integrity, and availability — asking whether technical vulnerabilities could enable unauthorized access to ePHI.
- Health data as near-universal DPIA trigger under GDPR — Because health data is classified as a special category of personal data, virtually all health data processing activities qualify as high-risk under GDPR's DPIA trigger criteria. Healthcare organizations cannot avoid DPIA requirements by limiting the scale of their processing; the sensitivity of the data category itself activates the requirement regardless of processing volume.
- HIPAA's periodic and change-triggered assessment cycle — HIPAA's Security Risk Analysis must be conducted periodically and is additionally triggered by material system changes including new technology implementations, significant upgrades, and identified security incidents. The regulation requires "reasonable" safeguards tailored to the organization's size and complexity — a standard that provides implementation flexibility but must be justified in documentation.
- GDPR's accountability principle requiring documented evidence — GDPR Article 5's accountability principle requires organizations not only to comply with DPIA requirements but to document assessments in a manner that demonstrates compliance to supervisory authorities. The burden of proof lies with the organization — the absence of documentation is treated as evidence of non-compliance regardless of whether a DPIA was actually conducted.
- Unified risk assessment framework addressing both frameworks simultaneously — A harmonized risk assessment framework that addresses both GDPR's individual rights focus and HIPAA's system vulnerability focus can satisfy both requirements from a single assessment exercise — with GDPR's broader scope generally requiring more comprehensive analysis that covers HIPAA's more narrowly defined system vulnerability assessment. Organizations that tag data records with applicable regulatory jurisdiction at the point of collection can automatically apply the correct assessment processes.
- GDPR penalty exposure for DPIA failures reaching 4% of global turnover — Failing to conduct required DPIAs can result in GDPR penalties up to 4% of annual global turnover or €20 million, whichever is higher — the most severe penalty tier under GDPR's enforcement framework. Combined with HIPAA's penalty exposure for inadequate risk analysis, the combined regulatory consequence of failing to conduct required assessments represents a material financial risk for healthcare organizations subject to both frameworks.
How do GDPR's DPO requirement and HIPAA's Privacy and Security Officer requirements differ in independence, scope, and incident response responsibilities?
- DPO independence as GDPR's governance differentiator — The DPO's legally mandated independence — reporting directly to top management, protected from job-related risks during their duties, and free from conflicts of interest — distinguishes the GDPR governance model from HIPAA's operational officer roles. A DPO cannot be dismissed or penalized for performing their DPO functions, a protection that reflects GDPR's design as an independent oversight function rather than an operational management role.
- DPO as the supervisory authority liaison and individual rights coordinator — During a breach, the DPO coordinates with Data Protection Authorities, ensures GDPR's 72-hour notification deadline is met, serves as the contact point for individuals exercising data rights, and documents justifications for any notification delays. The DPO does not handle technical or forensic aspects of the breach response — their function is governance oversight and regulatory liaison, not technical remediation.
- HIPAA Privacy Officer's patient rights and notification responsibilities — The Privacy Officer is responsible for patient rights management, PHI permissible use compliance, patient communication during incidents, and notification requirement execution. This operational role requires expertise in healthcare privacy law and patient advocacy — skills distinct from the technical security expertise the Security Officer requires.
- HIPAA Security Officer's technical containment and forensic responsibilities — The Security Officer under Security Rule 164.308 is responsible for technical containment of security incidents, forensic investigation of ePHI breaches, risk analysis of breach scope and impact, and implementation and maintenance of technical safeguards. This role requires cybersecurity expertise and technical knowledge that are distinct from the legal and compliance expertise the Privacy Officer requires.
- Separation of Privacy and Security Officer roles for organizations over 500 employees — For healthcare organizations with 500 or more employees, maintaining distinct Privacy and Security Officer roles is recommended because the skill requirements — legal and patient advocacy expertise versus technical cybersecurity expertise — are sufficiently different that combining them in a single individual creates functional gaps in one dimension or the other. Organizations should also maintain documented succession plans for the Security Officer position to prevent compliance lapses if the role becomes vacant.
- External DPO as a cost-efficient option for smaller healthcare organizations — Smaller healthcare organizations subject to GDPR that cannot justify a full-time DPO can appoint an external consultant as DPO — a cost-efficient alternative that provides the required independence and expertise without the overhead of a permanent staff position. This option is unavailable under HIPAA, where the operational nature of the Privacy and Security Officer roles requires internal organizational ownership.
How should healthcare organizations integrate GDPR and HIPAA incident response requirements into a unified operational strategy?
- Unified response team activated within the first hour — A response team including IT, clinical, legal, and compliance experts should be activated within the first hour of incident detection, with roles pre-assigned and notification templates pre-drafted for both EU supervisory authorities and HHS. The first hour response activates the governance structure before timeline pressure creates coordination failures.
- GDPR's 72-hour rule as the universal default timeline — Setting GDPR's 72-hour window as the default for all incidents — regardless of whether EU residents are involved — eliminates parallel notification workflows, builds the organizational response culture that GDPR requires, and ensures HIPAA's 60-day deadline is always satisfied as a consequence of more demanding GDPR compliance.
- Phased GDPR notification enabling compliance under investigation pressure — Using GDPR's phased notification provision — submitting initial reports within 72 hours with available information and following up as investigation progresses — enables compliance with the strict timeline even when breach scope is still being determined. Pre-drafted initial notification templates with variable fields for incident-specific details enable rapid submission without waiting for complete investigation findings.
- Attorney-client privilege protection through legal routing of forensic reports — Routing forensic investigation and risk assessment reports through legal counsel preserves attorney-client privilege during regulatory inquiries or litigation — a protection that is available only if legal routing is established as standard incident response procedure rather than activated reactively after regulatory contact.
- State-specific deadline tracking alongside federal and EU obligations — State breach notification laws including New York's SHIELD Act with a 30-day reporting requirement impose timelines that may be stricter than either GDPR or HIPAA federal obligations. Dual compliance programs must track state-specific deadlines alongside EU supervisory authority and HHS obligations to prevent secondary notification failures.
- Data record tagging at collection enabling automated regulatory routing — Tagging data records with their applicable regulatory jurisdiction at the point of collection — EU personal data, U.S. PHI, or both — enables automated application of the correct risk assessment processes and notification requirements during incident response, preventing the classification ambiguity that delays notification decisions when both GDPR and HIPAA obligations may apply to the same breach.
How does Censinet RiskOps™ specifically address the automation, documentation, and coordination requirements of unified GDPR and HIPAA incident response?
- Automated data discovery pre-classifying PHI and special category health data — Censinet RiskOps™ provides automated data discovery and inventory tools that identify and classify PHI and GDPR special category health data in advance of incidents — preventing the last-minute classification delays that slow breach scope determination and push notification timelines past 72-hour GDPR requirements.
- Centralized risk landscape visibility across the full organization — The platform's centralized command center provides real-time visibility across the organization's risk landscape during active incidents — enabling the multidisciplinary response team to maintain a shared situational picture across IT, clinical, legal, and compliance functions rather than coordinating through fragmented information channels that introduce delay and inconsistency.
- Automated risk assessment quantifying individual harm for GDPR threshold determination — When a breach occurs, Censinet RiskOps™ automates the risk assessment process that determines whether the incident crosses GDPR's "high risk to individuals' rights and freedoms" threshold for individual notification and HIPAA's "low probability of PHI compromise" safe harbor determination — both threshold judgments that manual assessment processes resolve too slowly to meet GDPR's timeline.
- Pre-drafted notification templates integrated with case management — Pre-drafted notification templates for EU supervisory authorities, HHS, affected individuals, media outlets, and credit bureaus integrated with the platform's case management features enable rapid template completion and submission rather than document-from-scratch notification drafting under timeline pressure — a capability that directly addresses the first-hour response requirement.
- Comprehensive audit trails satisfying both EU and U.S. regulators — Censinet RiskOps™ maintains the comprehensive audit trails documenting incident detection, risk assessment decisions, notification actions, and remediation steps that both GDPR's accountability principle and HIPAA's documentation requirements demand. This unified audit trail serves both regulatory frameworks from a single evidence source.
- Replacing the manual error processes responsible for 74% of breaches — By automating the detection, documentation, and reporting workflows that manual processes handle inconsistently and error-prone, Censinet RiskOps™ directly addresses the manual error root cause responsible for approximately 74% of data breach incidents — converting the human error vulnerability in incident response from an ongoing exposure into a managed, automated compliance function.


